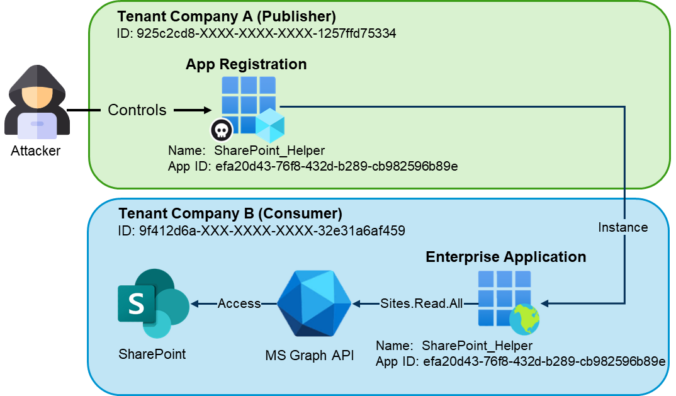
This post is part of a small blog series covering common Entra ID security findings observed during real-world assessments. Each article explores selected findings in more detail to support a clearer understanding of the underlying risks and practical implications. Introduction In the vast majority of tenants we review, there are enterprise applications that originate from […]
Compass Security Blog
Offensive Defense
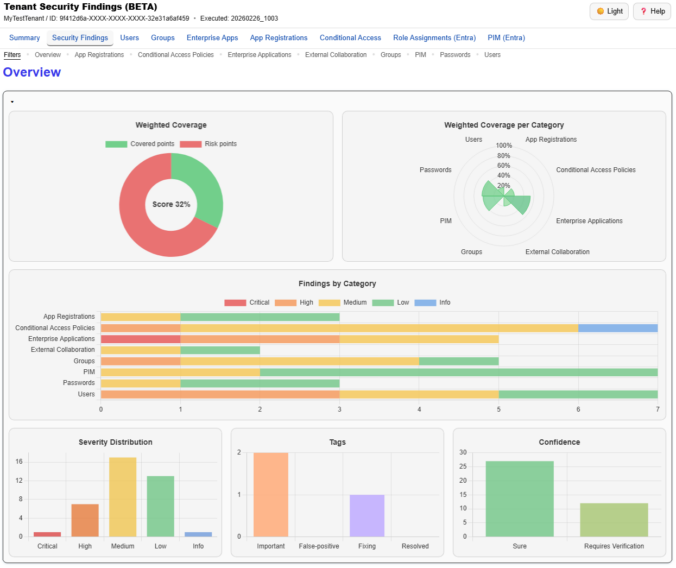
We just released a big update for EntraFalcon. The new Security Findings Report adds an interactive HTML overview to EntraFalcon that consolidates tenant settings and object-based checks into structured security findings. Over 60 checks, graphical charts, filtering, export, and more options are now available.
While not new, a self-referencing LNK file in combination with winget configuration instructions can be a viable initial access payload for environments where the Microsoft Store is not disabled.
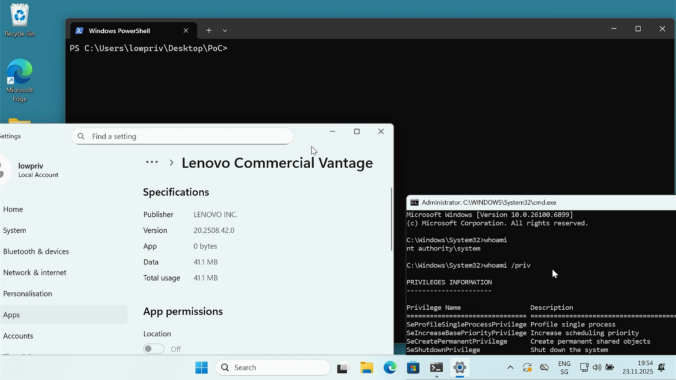
Last year we wrote about a Windows 11 vulnerability that allowed a regular user to gain administrative privileges. Not long after, Manuel Kiesel from Cyllective AG reached out to us after stumbling across a seemingly similar issue while investigating the Lenovo Vantage application. It turns out that the exploit primitive for arbitrary file deletion to gain SYSTEM privileges no longer works on current Windows machines.
Over the course of 2025, we performed several hundred security assessments for our clients. In each of these, security analysts must understand a new environment and often work with unfamiliar technologies. Even for well-known technologies, things change rapidly. Quick learning and adaptability are essential skills.
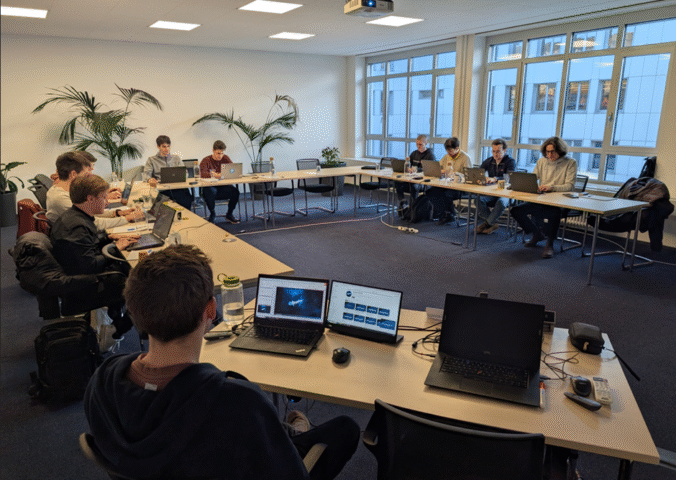
To keep our security analysts sharp and up to date, we regularly attend security conferences, external courses and trainings but also organize internal sessions. It has become a tradition for us to spend the first week of January learning new things, starting the year improving our know-how.
© 2026 Compass Security Blog