In part 2 of our 4-part series on common Entra ID security findings, we show how seemingly harmless group configurations can be abused to bypass security controls and gain high privileges.
The post shows scenarios where insufficiently protected groups are used to:
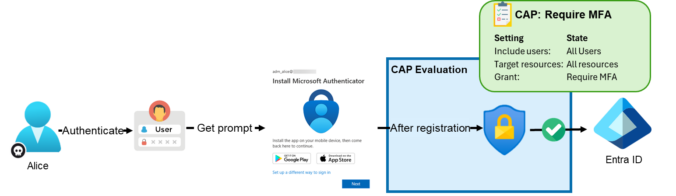
weaken Conditional Access protections for administrators
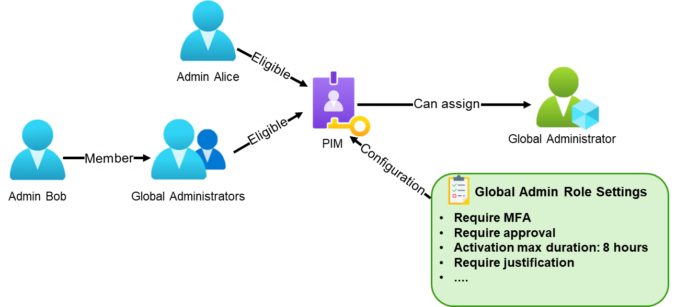
enable privilege escalation through PIM for Groups
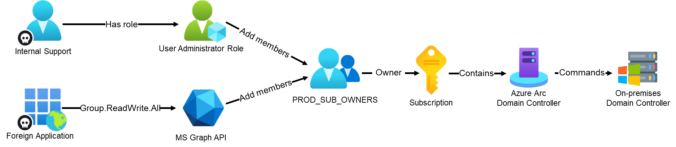
grant privileged access to Azure resources, leading to full compromise
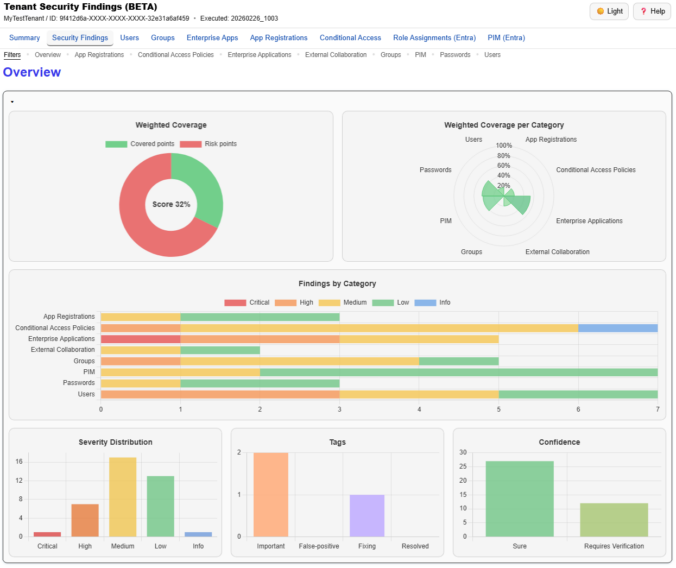
We also show how to detect these issues in practice using EntraFalcon and how to mitigate them.
Continue reading