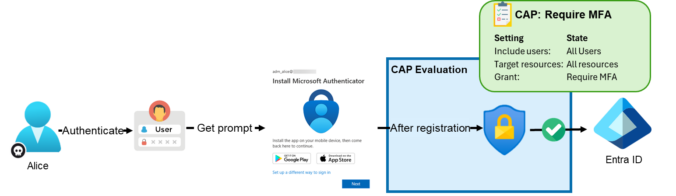
This post is part of a small blog series covering common Entra ID security findings observed during real-world assessments. Each article explores selected findings in more detail to provide a clearer understanding of the underlying risks and practical implications. Conditional Access Policies Conditional Access policies are among the most important security controls in Entra ID. […]
Compass Security Blog
Offensive Defense
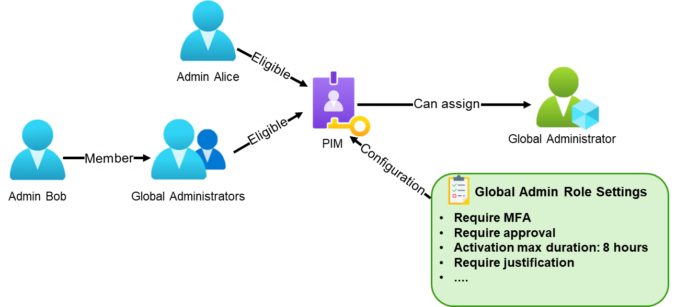
This post is part of a small blog series covering common Entra ID security findings observed during real-world assessments. Each article explores selected findings in more detail to provide a clearer understanding of the underlying risks and practical implications. What Is Privileged Identity Management? Privileged Identity Management (PIM) is a service in Microsoft Entra ID […]
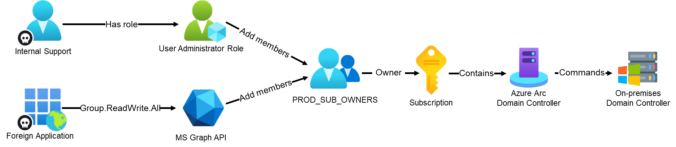
In part 2 of our 4-part series on common Entra ID security findings, we show how seemingly harmless group configurations can be abused to bypass security controls and gain high privileges.
The post shows scenarios where insufficiently protected groups are used to:
weaken Conditional Access protections for administrators
enable privilege escalation through PIM for Groups
grant privileged access to Azure resources, leading to full compromise
We also show how to detect these issues in practice using EntraFalcon and how to mitigate them.
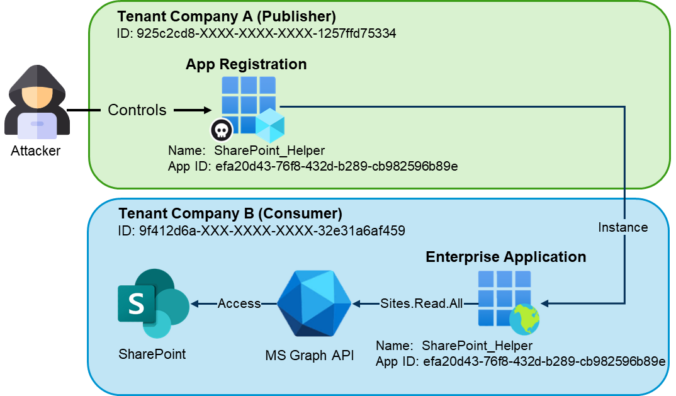
This post is part of a small blog series covering common Entra ID security findings observed during real-world assessments. Each article explores selected findings in more detail to support a clearer understanding of the underlying risks and practical implications. Introduction In the vast majority of tenants we review, there are enterprise applications that originate from […]
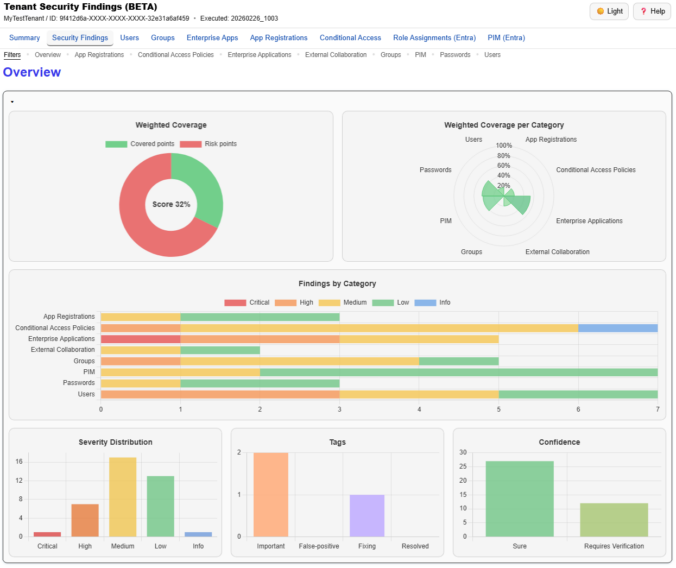
We just released a big update for EntraFalcon. The new Security Findings Report adds an interactive HTML overview to EntraFalcon that consolidates tenant settings and object-based checks into structured security findings. Over 60 checks, graphical charts, filtering, export, and more options are now available.
TL;DR: PowerShell tool to enumerate Entra ID objects, assignments and identify highly privileged objects or risky configurations. https://github.com/CompassSecurity/EntraFalcon Entra ID environments can contain thousands of objects – users, groups, service principals, and more – each with unique properties and complex relationships. While manual reviews through the Entra portal might be feasible in smaller environments, they […]
The anonymous data on our cases allows us to answer the question “What is a typical DFIR case at Compass Security?” and we conclude its the analysis, containment, eradication and recovery of one or a few devices in a Windows domain which is probably no surprise :)
More and more companies use Microsoft 365, well even we at Compass-Security use it internally. Moving to the cloud solves many issues that our DFIR team had to deal with in the past years. Managed infrastructure means no ProxyShell, Hafnium, etc. We’re grateful for that.
Email authentication and security is another complex topic that was often misconfigured in the past. We often could send phishing email in the name of our clients during assessments. Office 365 makes the life of scammers and phishers somehow harder. We’re also grateful for that.
However we still encounter some O365 environments where it’s possible to send spoofed emails. Why is that, you ask? We also wondered and dug into the O365 features and settings!
Recently, SANS Institute has published the 9th log management survey (2014). The paper identifies strengths and weaknesses in log management systems and practices. It further provides advice to improve visibility across systems with proper log collection, normalization and analysis. Log management is very important to Compass as it heavily influences forensic investigations. Evidently, accurate information […]
© 2026 Compass Security Blog