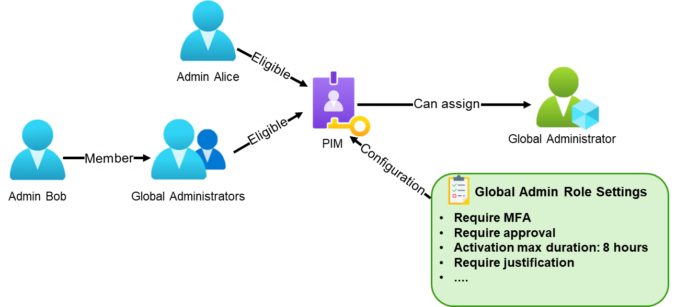
This post is part of a small blog series covering common Entra ID security findings observed during real-world assessments. Each article explores selected findings in more detail to provide a clearer understanding of the underlying risks and practical implications. What Is Privileged Identity Management? Privileged Identity Management (PIM) is a service in Microsoft Entra ID […]
Compass Security Blog
Offensive Defense
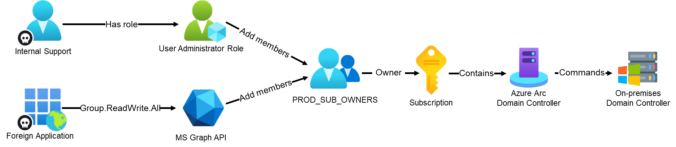
In part 2 of our 4-part series on common Entra ID security findings, we show how seemingly harmless group configurations can be abused to bypass security controls and gain high privileges.
The post shows scenarios where insufficiently protected groups are used to:
weaken Conditional Access protections for administrators
enable privilege escalation through PIM for Groups
grant privileged access to Azure resources, leading to full compromise
We also show how to detect these issues in practice using EntraFalcon and how to mitigate them.
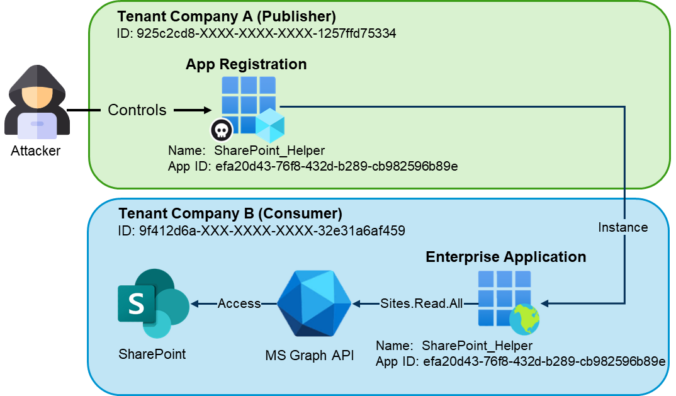
This post is part of a small blog series covering common Entra ID security findings observed during real-world assessments. Each article explores selected findings in more detail to support a clearer understanding of the underlying risks and practical implications. Introduction In the vast majority of tenants we review, there are enterprise applications that originate from […]
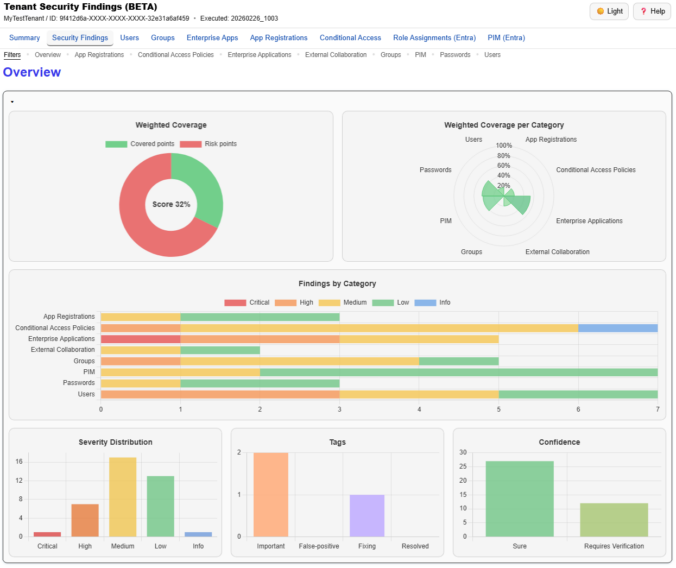
We just released a big update for EntraFalcon. The new Security Findings Report adds an interactive HTML overview to EntraFalcon that consolidates tenant settings and object-based checks into structured security findings. Over 60 checks, graphical charts, filtering, export, and more options are now available.
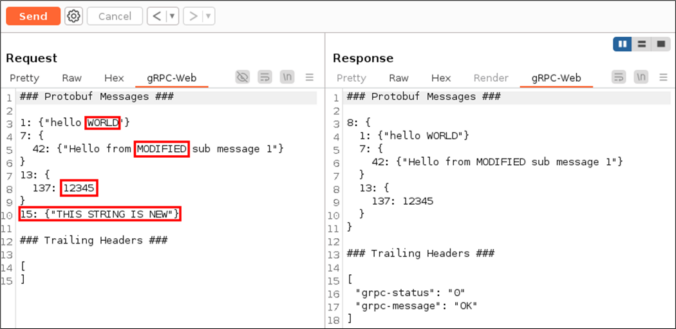
The gRPC framework, and by extension gRPC-Web, is based on a binary data serialization format. This poses a challenge for penetration testers when intercepting browser to server communication with tools such as Burp Suite.
This project was initially started after we unexpectedly encountered gRPC-Web during a penetration test a few years ago. It is important to have adequate tooling available when this technology appears. Today, we are releasing our Burp Suite extension bRPC-Web in the hope that it will prove useful to others during their assessments.
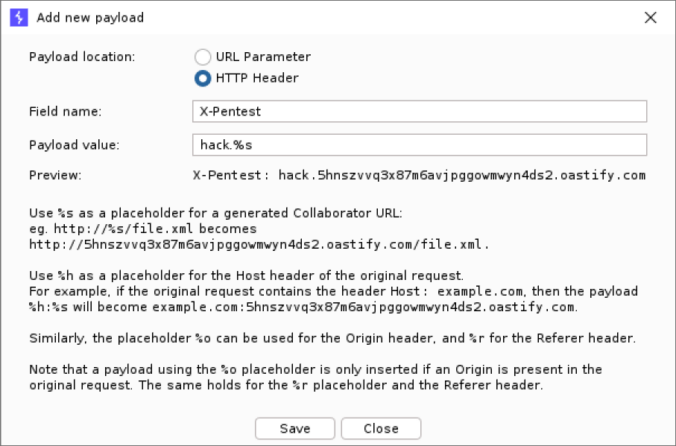
Collaborator Everywhere is a well-known extension for Burp Suite Professional to probe and detect out-of-band pingbacks.
We developed an upgrade to the existing extension with several new exiting features. Payloads can now be edited, interactions are displayed in a separate tab and stored with the project file. This makes it easier to detect and analyze any out-of-band communication that typically occurs with SSRF or Host header vulnerabilities.
In 2024 we looked at the possibility of leveraging open weights LLMs for source code analysis. The answer was clearly negative, as a small code base could easily take 200K tokens, more than any context window offered by open weights models. The table below summarizes the top LLMs by context window as of today. Context […]
TL;DR: PowerShell tool to enumerate Entra ID objects, assignments and identify highly privileged objects or risky configurations. https://github.com/CompassSecurity/EntraFalcon Entra ID environments can contain thousands of objects – users, groups, service principals, and more – each with unique properties and complex relationships. While manual reviews through the Entra portal might be feasible in smaller environments, they […]
This blog post introduces our new custom queries for BloodHound Community Edition (CE) and explains how you can use them effectively to analyze your Active Directory infrastructure. TL;DR: Check out our new BloodHound CE custom queries! Active Directory and BloodHound The majority of our customers run a Microsoft Active Directory infrastructure, either exclusively on-prem or […]
TLDR: Scan GitLab job logs for credentials using https://github.com/CompassSecurity/pipeleak Many organizations use (self-hosted) GitLab instances to manage their source code and a lot of infrastructure is managed in code (IaC), thus these configurations must be source-controlled as well, putting a lot of responsibility on the source code platform in use. Often deployments are automated using CI/CD […]
© 2026 Compass Security Blog