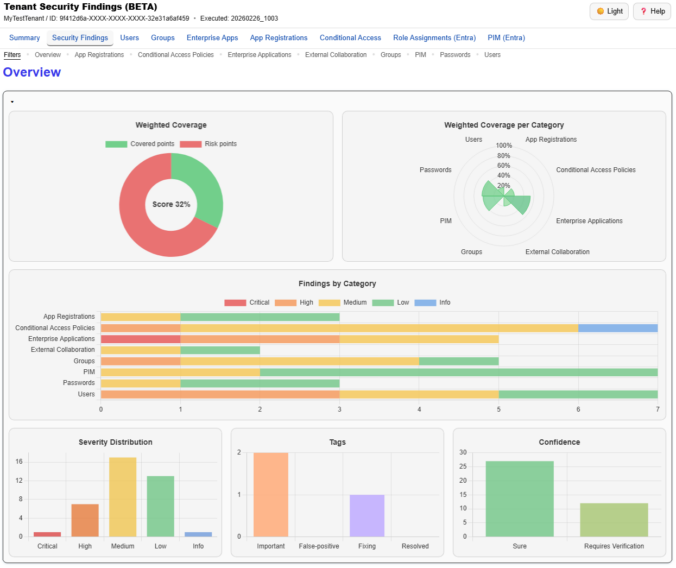
We just released a big update for EntraFalcon. The new Security Findings Report adds an interactive HTML overview to EntraFalcon that consolidates tenant settings and object-based checks into structured security findings. Over 60 checks, graphical charts, filtering, export, and more options are now available.
Compass Security Blog
Offensive Defense
TL;DR: PowerShell tool to enumerate Entra ID objects, assignments and identify highly privileged objects or risky configurations. https://github.com/CompassSecurity/EntraFalcon Entra ID environments can contain thousands of objects – users, groups, service principals, and more – each with unique properties and complex relationships. While manual reviews through the Entra portal might be feasible in smaller environments, they […]
As a defender, you want to find and patch attack paths in your Active Directory environment. One cannot easily spot issues by looking at the Active Directory Users and Computers console, GPOs, etc. but here comes BLOODHOUND.
We have shortly described the Lync federations in a previous post. With the usage of federations the question comes about the privacy and the security of the user’s information (e.g. presence information). There are scenarios where an employee doesn’t answer the phone but is mentioned as “available” in Lync. This could lead to a misunderstanding […]
Microsoft Lync Server (a combination of “link” and “sync”, see [6]) communications software offers instant messaging (IM), presence, conferencing, and telephony solutions. Lync can be integrated with SharePoint or Exchange to extend its functionalities. Users can e.g. search for specific skills within the Lync client when SharePoint integration is enabled. Exchange is used as a […]
© 2026 Compass Security Blog