Collaborator Everywhere is a well-known extension for Burp Suite Professional to probe and detect out-of-band pingbacks.
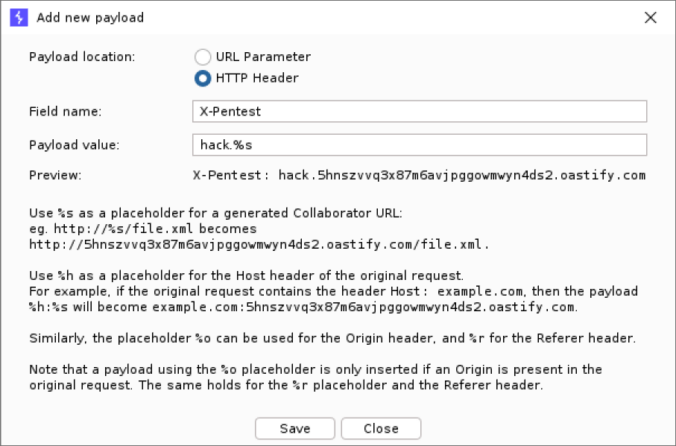
We developed an upgrade to the existing extension with several new exiting features. Payloads can now be edited, interactions are displayed in a separate tab and stored with the project file. This makes it easier to detect and analyze any out-of-band communication that typically occurs with SSRF or Host header vulnerabilities.