What is a Hack-Lab?
Compass Security provides a monthly playful occasion for the security analysts to get-together and try to hack new devices, dive into current technologies and share their skills with their fellow analysts.
Topics
The following topics, tools, and technology has been discussed during this Hack-Lab:
- Cold Boot Attacks,
- Fake Mails,
- Tool Development,
- OSINT
Wrap-Up
Topic #1 – Cold Boot Attacks
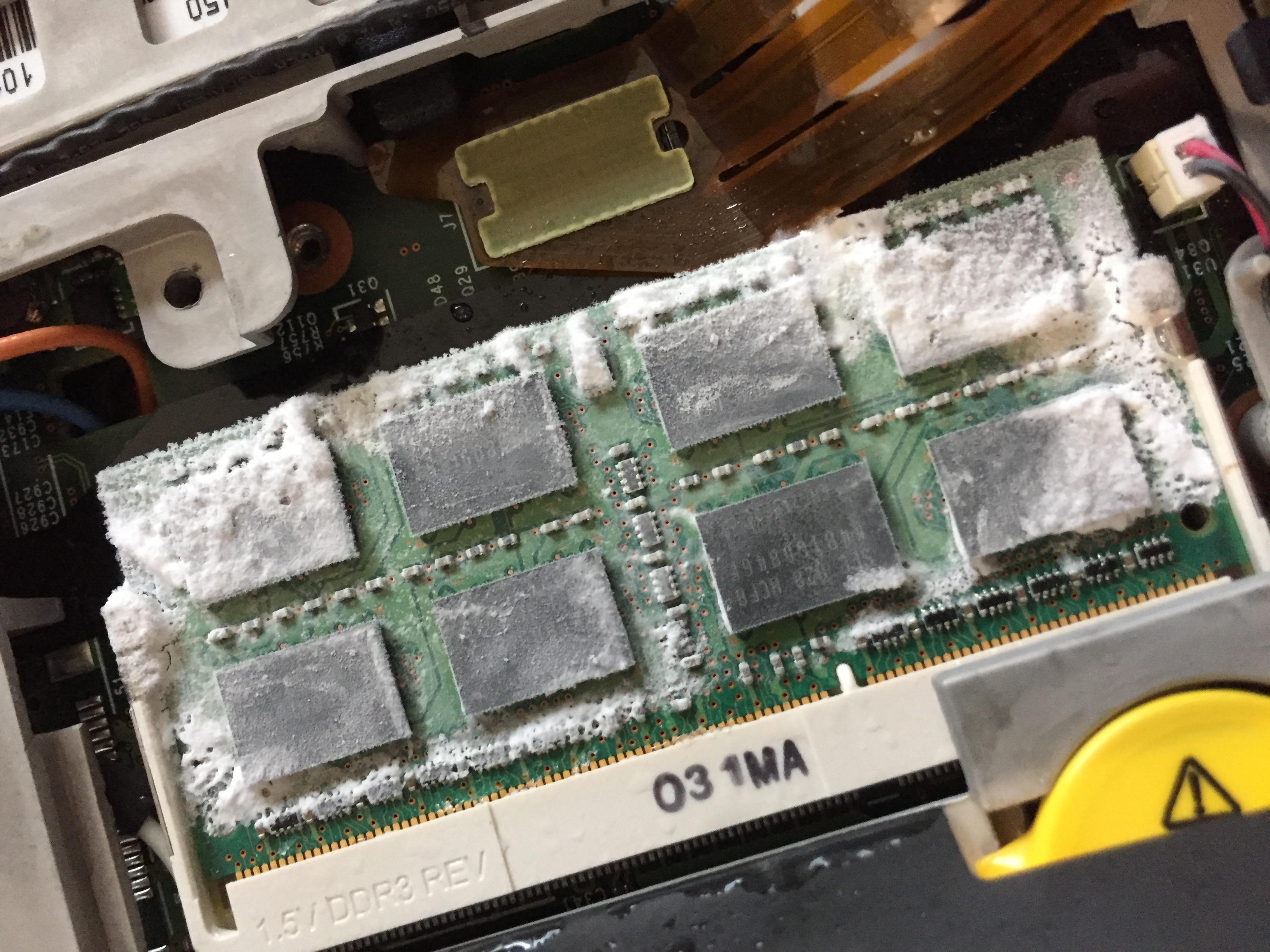
The cold boot attack was first described in 2008 [1]. The attack allows to extract sensitive information, such as encryption keys from RAM by inserting them on an other system. Physically cooling down the memory extends the lifetime of the stored data.
A successful attack could allow to dump Bitlocker encryption keys of a stolen computer, if there is no pre-boot authentication. Microsoft commented the cold boot research paper [2] with the following conclusion:
Because of these factors, this type of attack is rarely possible on modern devices. Even in cases where the risk factors exist on legacy devices, attackers will find the attack unreliable.
[…]
The BitLocker pre-boot authentication feature can successfully mitigate memory remanence attacks on most devices, but you can also mitigate such attacks by protecting the system UEFI or BIOS and prevent the PC from booting from external media (such as a USB flash drive or DVD). The latter option is often a better choice, because it provides sufficient protection without inconveniencing users with pre-boot authentication.
Therefore, we decided to attempt cold boot attacks to verify if pre-boot authentication is still advisable on newer devices.
We have not yet attempted to recover the encryption keys, but our initial tests revealed that the memory definitely retains some of the stored bits even with newer, faster RAM.
At the current stage, we still believe pre-boot authentication is the way to go for the following reasons:
- Reading contents from the memory does not need to be reliable, as an attacker can repeat the booting process several times, gradually approaching the right Bitlocker key
- SecureBoot does not prevent the attack, since the memory can be extracted and inserted into another device, without needing to boot from an alternative OS.
- If the device contains memory with bad data remanence properties, the memory can be replaced with a compatible module that allows cold boot attacks more reliably.
We will continue investigating cold boot attacks in future, so stay tuned.
[1] https://citp.princeton.edu/research/memory/
Topic #2 – Fake Mails
Nearly every time we perform a phishing campaign, we can successfully spoof the e-mail sender address in the “From:” field of the mail message. During the Hack-Lab we therefore decided to take a look at the existing techniques that would allow to successfully identify and block spoofed mails.
Keywords
- Envelope From (RFC 5321)
- From Header (RFC 5322)
- DKIM (RFC 6376)
- SPF (RFC 7208)
- DMARC (RFC 7489)
Topic #3 – Tool Development
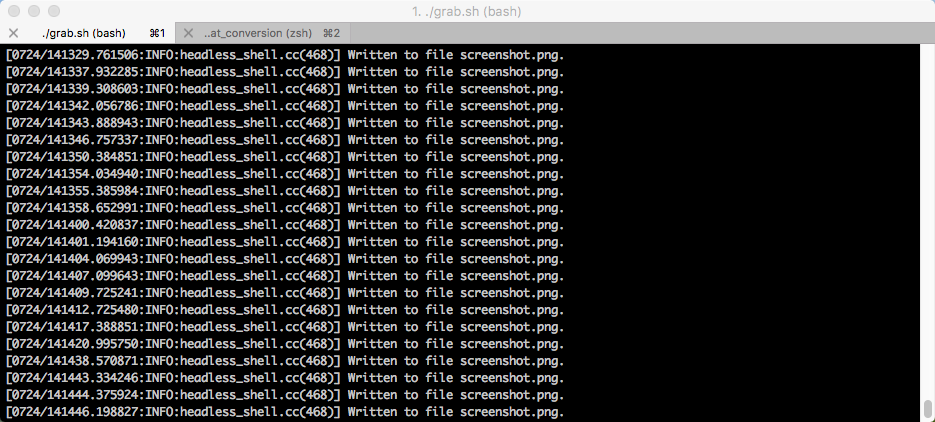
The goal of this topic was to write an internal tool to help with performing a few repetitive tasks such as URL extraction, creating screen shots of collected URLs and preparing the information for further comparison and monitoring purposes. Until recently PhantomJS was, according to PhantomJS itself, the “optimal solution for programmatically capture web content”. However, since Chrome has recently received a headless mode, we decided to play around with that option instead.
Used Technology
- Phantom JS
- Google Chrome in Headless Mode
Topic #4 – OSINT
In prevision for future customer projects, various tools to perform open source research have been tested. Among them were Maltego, Aquatone and datasploit. Focus was put on the search for IP ranges, domains, and sub-domains as well as employee data (email, phone number, personal information). The tools and manual Internet searches (Google hacking) have proven useful in revealing information that can be used in a future penetration test or phishing campaign.
Leave a Reply