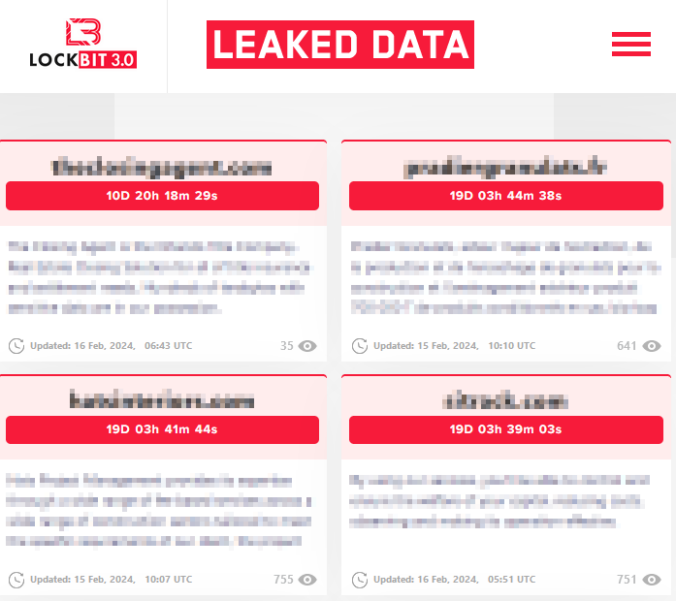
Something a bit wild happened recently: A rival of LockBit decided to hack LockBit. Or, to put this into ransomware-parlance: LockBit got a post-paid pentest. It is unclear if a ransomware negotiation took place between the two, but if it has, it was not successful. The data was leaked.
Now, let’s be honest: the dataset is way too small to make any solid statistical claims. Having said that, let’s make some statistical claims!