Sometimes, it doesn’t take much for a good scam: a good story, a little persuasion, then disappear again… and sometimes, the scammers come up with tactics that come straight out of the textbook.
Compass Security Blog
Offensive Defense
Page 2 of 2
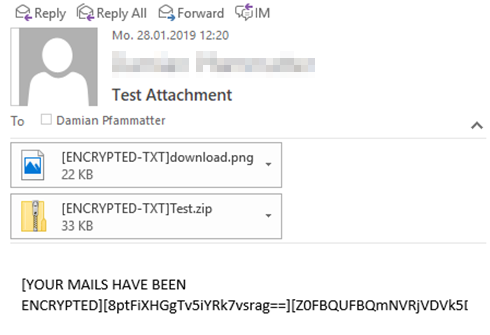
Ransomware focuses on encrypting data on a filesystem-level, either locally on infected client systems or remotely on accessible file servers. However, what if ransomware would start encrypting data on an application-level too?
Contents Introduction Background Story External Device Access Auditing with Windows Security Event Logs Audit Plug and Play Activity Audit Removable Storage Activity External Device Access Auditing with Default Windows Artifacts Other Ways to Monitor External Device Usage Conclusion References Introduction Have you ever investigated a data leakage case involving a suspect potentially leaking data to […]
Present State of Affairs We have been teaching forensics and network incident analysis for quite a while. We have investigated into a reputable number of cases and we are not the only doing so. Hence, one would expect a certain degree of automation in analysis. However, the high frequency of software release cycles somehow leads […]
© 2026 Compass Security Blog