On paper, the vast majority of crisis plans look reasonable, actionable and complete. Once the rubber hits the road, however, chaos emerges quickly.
Compass Security Blog
Offensive Defense
Over the past few years, we have had the opportunity to conduct several Purple Teaming exercises together with our customers.
Particularly after Purple Teaming exercises involving external providers, we often see a mismatch between the customer’s expectations and the service provided.
This blog post attempts to summarize how to prevent the most prevalent issues with a managed security service as early as possible.
This is hopefully the most useless blog post you will read this year as this post will detail our experience dealing with ransomware cases. It is one of the most common reasons why we get called in to help and it has become a big business. Chainalysis, for example, has tracked $1.1 billion in ransomware […]
The anonymous data on our cases allows us to answer the question “What is a typical DFIR case at Compass Security?” and we conclude its the analysis, containment, eradication and recovery of one or a few devices in a Windows domain which is probably no surprise :)
One of the rare cases where we can decrypt and recover files following-up with a ransomware attack.
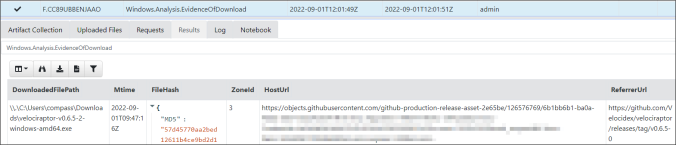
This post provides ideas of processes to follow and gives basic guidance on how to collect, triage and analyze artifacts using Velociraptor
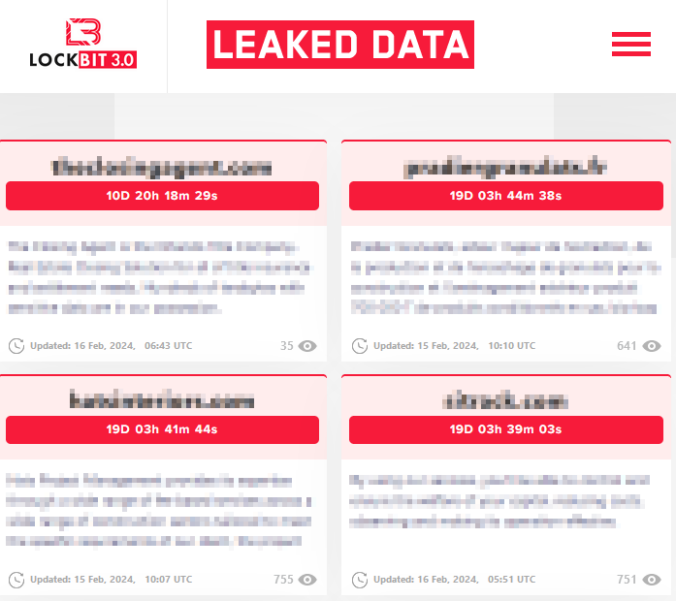
During a DFIR (Digital Forensics and Incident Response) Case, we encountered an ESXi Hypervisor that was encrypted by the Ransomware LockBit 2.0. Suspicious SSH logons on the Hypervisor originated from an End-of-Life VPN Appliance (SonicWall SRA 4600). It turns out, this was the initial entry point for the Ransomware attack. Follow us into the forensics […]
Sometimes one goes deep down the rabbit hole, only to notice later that what we were looking for is just under one’s nose.
This is the story of a digital forensic analysis on a Linux system running docker containers. Our customer was informed by a network provider that one of his system was actively attacking other systems on the Internet. The system responsible for the attacks was identified and shut down.
Our DFIR hotline responded to the call and we were provided with a disk image (VMDK) to perform a digital forensic analysis.
Intro into a Compass Splunk App, which can be used to perform a first triage and high level analysis of Volatility results coming from multiple hosts.
The article discusses the very basics to keep systems ready for analysis of lateral movement. We present some guidelines in form of a cheat sheet and a tool (Readinizer) that you can run, to ensure that everything is set up as in the guidelines provided.
© 2026 Compass Security Blog