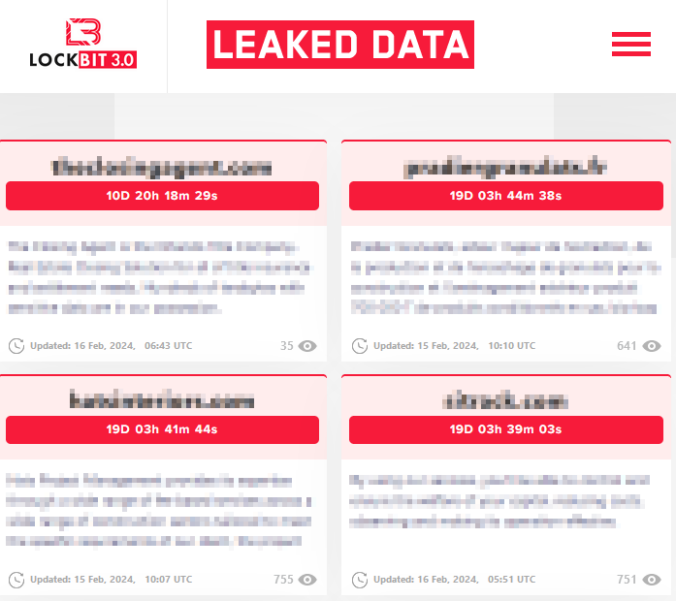
This is hopefully the most useless blog post you will read this year as this post will detail our experience dealing with ransomware cases. It is one of the most common reasons why we get called in to help and it has become a big business. Chainalysis, for example, has tracked $1.1 billion in ransomware […]
Compass Security Blog
Offensive Defense
Page 6 of 30
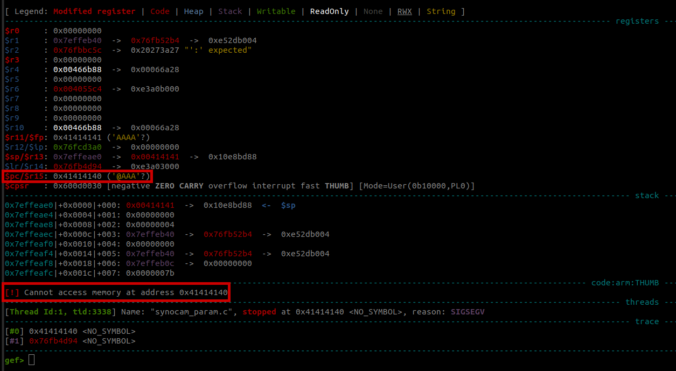
In this final part of this series, we are finally going to explain how the stack-based buffer overflow vulnerability can be exploited to gain unauthenticated remote code execution (RCE) on the Synology BC500 camera.
In this fourth part of the series, we analyze the memory corruption identified previously and manage to overwrite the program pointer!
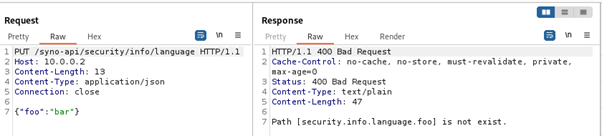
In this third part of the series, we focus on the exposed web services running on TCP ports 80 and 443.
Since a valid exploit chain must achieve code execution without prior authentication, we focus on the available functionality that can be accessed without authentication.
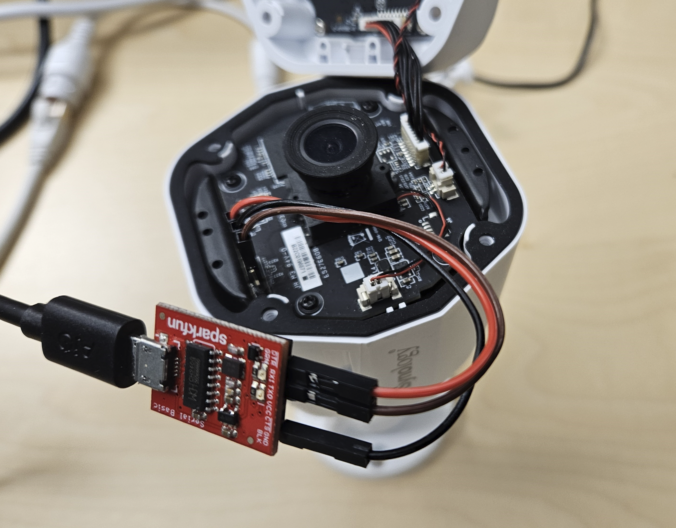
In this second blog post of the series, we start with the reconnaissance phase on the camera, a crucial step in understanding our target.
The aim here is to gather information about the target and identify potential vulnerabilities.
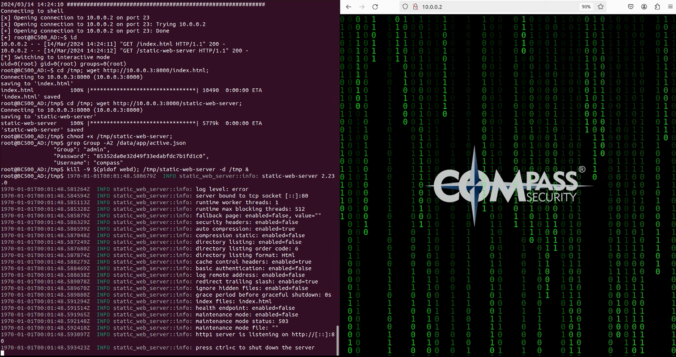
Around a year ago a few Compass analysts watched a talk at the Insomni’Hack conference about the Pwn2Own contest.
This is when they decided to take part! In this blog post, they talk about how they picked their target, got the firmware from the camera, and got into the shell.
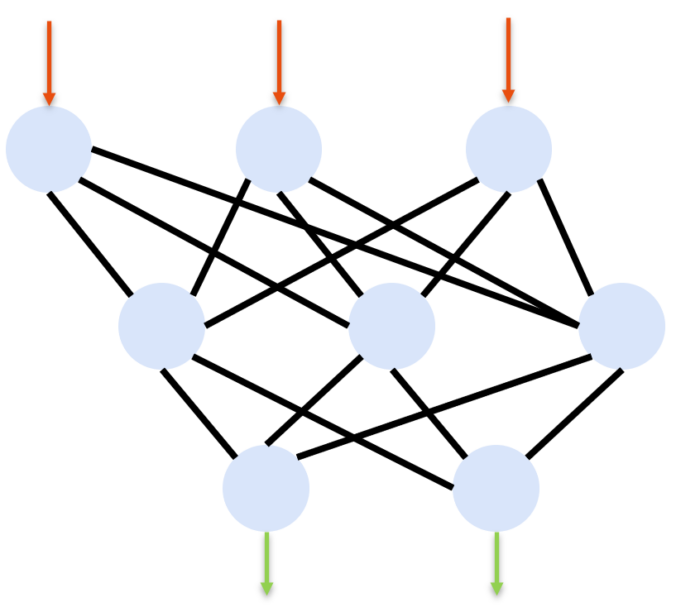
What are LLMs LLMs (Large Language Models) are language models with a large number of parameters. These parameters are the model’s variables, which it learns during training. Typically, this training is unsupervised learning on a large data set, during which the algorithm tries to find patterns in the provided data. The more it learns, the […]
In today’s interconnected world, it is a well-known fact that systems with Internet exposure are under continual threat of cyber-attacks. This risk extends from private websites to corporate infrastructure. With the increasing modernization of Industrial Control Systems (ICS), these vital components also become more exposed to such threats. But what is the extent and nature […]
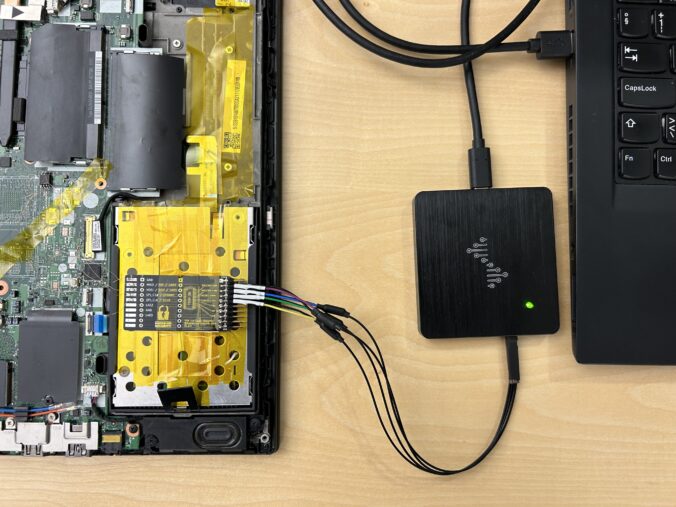
In this blog article, we would like to share key insights from the “Defeating Microsoft’s Default BitLocker Implementation” security training by Hands-On Security and emphasize the potential risks and consequences associated with this attack technique. Our target audience includes businesses looking to safeguard sensitive data on their Windows devices, as well as individuals with an elevated requirement for protecting their data.
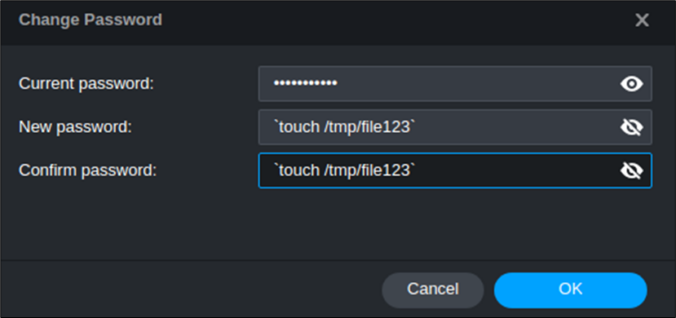
TL;DR An attacker is able to register new security keys (FIDO) or other authentication methods (TOTP, Email, Phone etc.) after a successful device code phishing attack. This allows an attacker to backdoor the account (FIDO) or perform the self-service password reset for the account with the newly registered sign-in methods. Microsoft deemed this not a vulnerability.
© 2026 Compass Security Blog