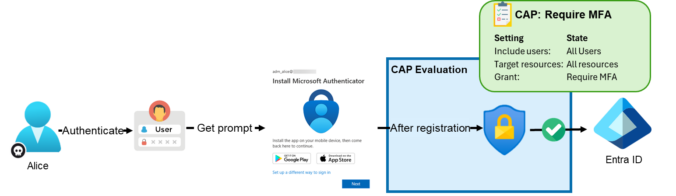
This post is part of a small blog series covering common Entra ID security findings observed during real-world assessments. Each article explores selected findings in more detail to provide a clearer understanding of the underlying risks and practical implications. Conditional Access Policies Conditional Access policies are among the most important security controls in Entra ID. […]
Compass Security Blog
Offensive Defense
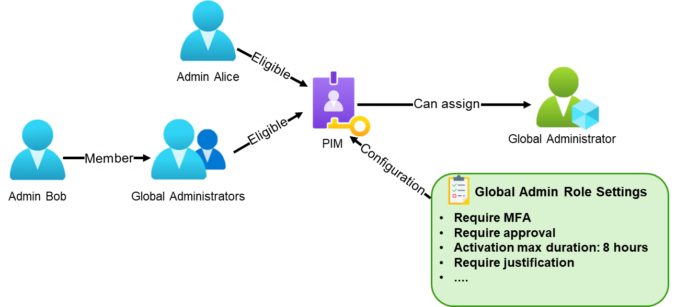
This post is part of a small blog series covering common Entra ID security findings observed during real-world assessments. Each article explores selected findings in more detail to provide a clearer understanding of the underlying risks and practical implications. What Is Privileged Identity Management? Privileged Identity Management (PIM) is a service in Microsoft Entra ID […]
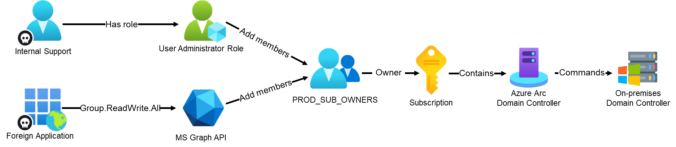
In part 2 of our 4-part series on common Entra ID security findings, we show how seemingly harmless group configurations can be abused to bypass security controls and gain high privileges.
The post shows scenarios where insufficiently protected groups are used to:
weaken Conditional Access protections for administrators
enable privilege escalation through PIM for Groups
grant privileged access to Azure resources, leading to full compromise
We also show how to detect these issues in practice using EntraFalcon and how to mitigate them.
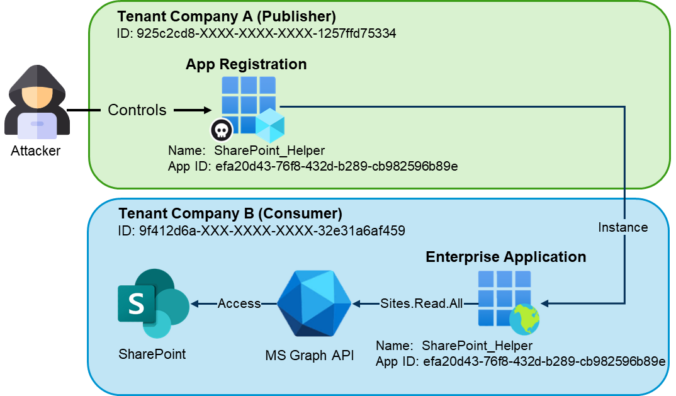
This post is part of a small blog series covering common Entra ID security findings observed during real-world assessments. Each article explores selected findings in more detail to support a clearer understanding of the underlying risks and practical implications. Introduction In the vast majority of tenants we review, there are enterprise applications that originate from […]
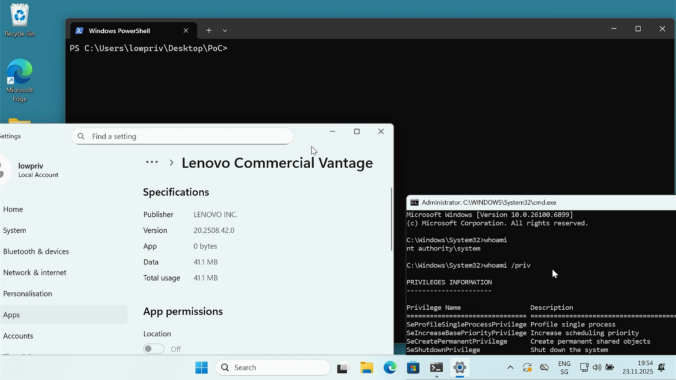
Last year we wrote about a Windows 11 vulnerability that allowed a regular user to gain administrative privileges. Not long after, Manuel Kiesel from Cyllective AG reached out to us after stumbling across a seemingly similar issue while investigating the Lenovo Vantage application. It turns out that the exploit primitive for arbitrary file deletion to gain SYSTEM privileges no longer works on current Windows machines.
Introduction As you may know, Compass Security participated in the 2023 edition of the Pwn2Own contest in Toronto and was able to successfully compromise the Synology BC500 camera using a remote code execution vulnerability. If you missed this, head over to the blog post here https://blog.compass-security.com/2024/03/pwn2own-toronto-2023-part-1-how-it-all-started/ Unfortunately, the same vulnerability was also identified by other […]
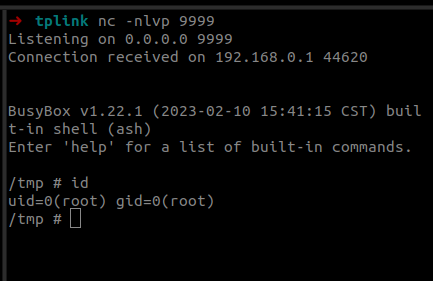
Last year we participated in the Pwn2Own 2023 Toronto competition and successfully exploited the Synology BC500 camera. The DEVCORE Internship Program team managed to exploit a bug in the TP-Link Omada Gigabit VPN Router. So I was naturally curious and wanted to figure out how difficult it would be to recreate that exploit having access only to a high-level bug description and the firmware.
What are LLMs LLMs (Large Language Models) are language models with a large number of parameters. These parameters are the model’s variables, which it learns during training. Typically, this training is unsupervised learning on a large data set, during which the algorithm tries to find patterns in the provided data. The more it learns, the […]
A journey into the discovery of privilege escalation vulnerabilities in the Lenovo Update process.
Passwordless products promise greater security and convenience by allowing users to log in to Windows systems with only their smartphone. But what is going on behind the scenes and how could a domain’s security stance be worsened by such a solution? In this post I will explain how these products are implemented and detail the vulnerabilities and weaknesses discovered in three tested products.
© 2026 Compass Security Blog