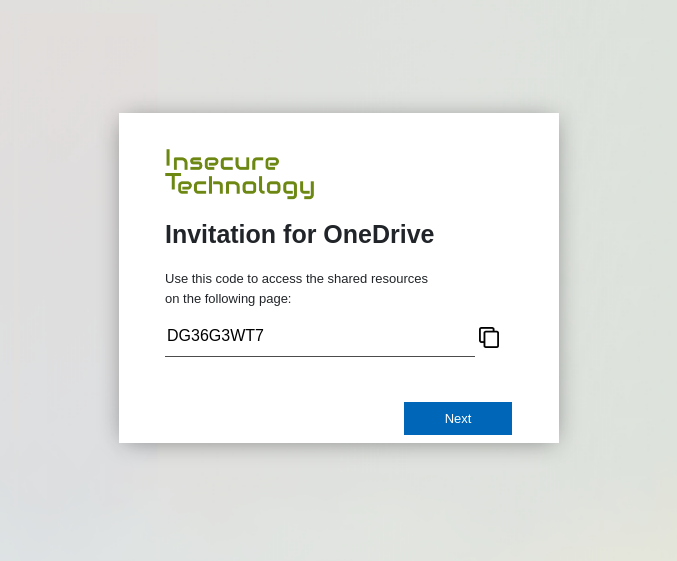
Device code phishing is nothing new. In fact it has been around for some years now. Despite the awesome capabilities of device code phishing, it is not widely used by threat actors. Therefore, it probably does not receive much attention from Microsoft. Compass Security is releasing two tools that can work hand in hand in a device code phishing exercise or even your next red team engagement.
Compass Security Blog
Offensive Defense
On October 12th the Swiss Cyber Storm conference took place in the Kursaal in Bern. Several Compass analysts attended the conference, our security analyst Yves Bieri held a talk and we also had a booth. The conference was great fun, finally a in-person conference with many interesting talks. This blog post wraps up some talks we attended.
“I love hacking can be used for the greater good.” During the Solothurn Film Festival 2020 we had the opportunity to meet Jim McKay, who directed, among others, two episodes for Mr. Robot season one. Jim had also time for a short interview. What is important for you working as a director/writer? Jim McKay: I […]
Contents Introduction Attack Overview Step-by-Step Detection Email Clients Administration Tools Exchange Compliance Features MAPI Editor Eradication Microsoft Security Response Center Swiss Cyber Storm 2018 Conclusion References Introduction In recent investigations, Compass recognized a raise in popularity for attackers to compromise Microsoft Exchange credentials. As one of the first steps after having obtained the credentials (most […]
Introduction Last Friday and Saturday (15./16. June 2018), the 6th edition of the security conference Area41 (formerly Hashdays, https://area41.io/) organized by DEFCON Switzerland (https://www.defcon-switzerland.org/, https://twitter.com/defconCH) took place in Zürich. Every Compass security analyst can attend two conferences every year supported by Compass. So most of the analysts decided to go to the Area41 this year […]
We are at the Area 41 conference! This IT Security Conference is happening on the 15/16th of June in 2018 in Zürich. Compass Security supports this non-profit event as Platinum Sponsor. We’ll have a Compass Booth where we discuss current topics with you – and how you can join our team as ethical hacker! The […]
What is CodeMash? CodeMash is a conference for software developers and IT security professionals. It takes place every year in Sandusky, Ohio, in the U.S. The event consists of two parts: two days of training sessions (called “PreCompiler”), followed by two days of conference with sessions. It attracts about 3’000 visitors and takes place in […]
At the beginning of August, as every year, two of our security analysts attended the most renowned IT security conferences Black Hat USA and DEF CON to learn about the latest trends and research. This year’s Black Hat conference, the 19th edition, took place at the Mandalay Bay Conference Center while DEF CON 24 was located […]
Compass Security recently presented its Windows Phone and Windows 10 Mobile research at the April 2016 Security Interest Group Switzerland (SIGS) event in Zurich. The short presentation highlights the attempts made by our Security Analysts to bypass the security controls provided by the platform and further explains why bypassing them is not a trivial undertaking. Windows 10 Mobile, which […]
Compass Security invested quite some time last year in researching the security of single sign-on (SSO) implementations. Often SAML (Security Assertion Markup Language) is used to implement a cross-domain SSO solution. The correct implementation and configuration is crucial for a secure authentication solution. As discussed in earlier blog articles, Compass Security identified vulnerabilities in SAML […]
© 2026 Compass Security Blog