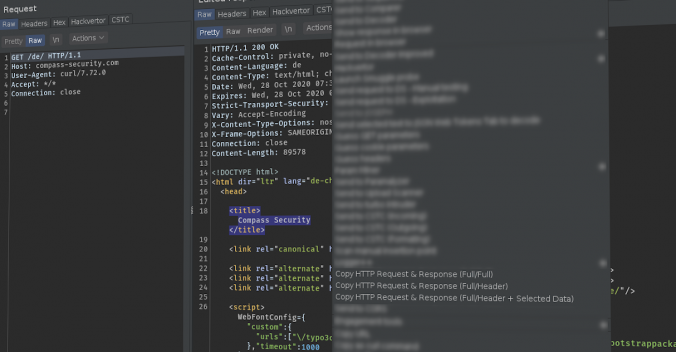
Writing good reports is key in penetration tests / security assessments, since this is the final result delivered to the customer. Vulnerabilities should be described in a way so that the customer can understand and also reproduce the issue. For web application pentests, the best way is often to show the HTTP requests and responses to explain an issue. This Burp Suite extension “Copy Request & Response” can assist you while the report.
Compass Security Blog
Offensive Defense
Page 2 of 6
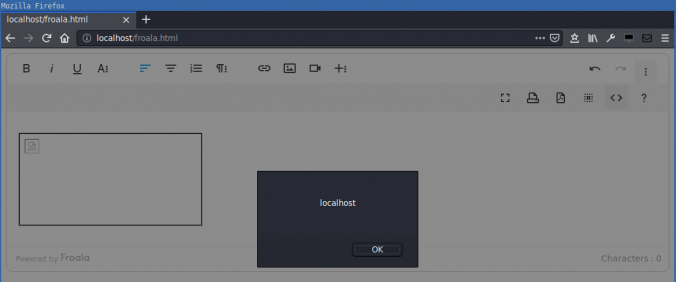
Compass found a DOM-based cross-site scripting (XSS) in the Froala WYSIWYG HTML Editor. HTML code in the editor is not correctly sanitized when inserted into the DOM. This allows an attacker that can control the editor content to execute arbitrary JavaScript in the context of the victim’s session.
A write-up of the OWASP Toronto January talk which mainly focused on the correlation and integration of results generated by automated tools in application security such as SAST, DAST and SCA. Alexandre Larocque concludes whether old-fashioned PDF reports are still worth it.
Mobile applications nowadays make heavy use of WebViews in order to render their user interfaces. Frameworks such as PhoneGap / Apache Cordova are even used to implement most of the application’s functionalities using WebViews only.
While native code, both in Android and in iOS, can quickly be analyzed using dynamic analysis tools like Frida, operations performed in WebViews cannot be easily debugged with the same methods.
This post is intended to explain what you typically want to check for during an OpenID Connect assessment and also provide you with a guide to setup your own OpenID Connect test environment.
Perfect Forward Secrecy (PFS) is a concept in Transport Layer Security (TLS) that makes sure that even if attackers manage to gain access to the private key of a certificate, they are not able to decrypt communication from the past (or communication in the future, without using active man in the middle attacks). Or in other […]
SharePoint is a very popular browser-based collaboration and content management platform. Due to its high complexity, proprietary technology and confusing terminology it is often perceived as a black-box that IT and security professionals do not feel very comfortable with. These days, web security topics are well understood by many security professionals, penetration testers and vendors. But what […]
Opening up an internal SharePoint farm to the Internet in order to share resources with external parties might seem a good idea, because it helps avoiding expensive infrastructure changes. However, in terms of security, this is not recommended because it does not sufficiently protect internal resources from external threats. The protection of internal resources hinges […]
What is a Hack-Lab? Compass Security provides a monthly playful occasion for the security analysts to get-together and try to hack new devices, dive into current technologies and share their skills with their fellows. This also includes the improvement of internal tools, the research of newly identified publicly known attacks, and security analysis of hardware […]
To achieve better-looking, more feature-rich and responsive applications, there is an ever-growing need to include resources from 3rd party domains into your web application. Common examples are JavaScript frameworks like jQuery or AngularJS, often distributed via a content delivery network (CDN), or even complete applications like Google Maps. But by including these resources, the security […]
© 2026 Compass Security Blog